Ask questions which are clear, concise and easy to understand.
Ask QuestionPosted by Aman Darbar? 7 years ago
- 0 answers
Posted by Rahul Chaudhary 7 years ago
- 1 answers
Posted by Sujata Murmu 7 years ago
- 2 answers
Posted by Aditya Kumar 7 years ago
- 4 answers
Posted by Nazeema Gaffar 7 years ago
- 1 answers
Yogita Ingle 7 years ago
A computer virus is a type of computer program that can replicate itself by making copies of itself by making copies of itself without the user's knowledge or consent.
Computer virus spread from following ways
i. Opening the infected email attachment.
ii. By downloading infected programs from the internet.
iii. By using infected floppy disk, pen drives and CDs.
iv. By transferring an infected program over a network and executing it.
Posted by Abhijeet Soni 7 years ago
- 1 answers
Yogita Ingle 7 years ago
| Full form | Carbon Copy. | Blind Carbon Copy. |
| Working | A recipient of Cc field is visible to the primary recipients of To: field, other recipients of Cc and recipients of Bcc field. | A recipient of Bcc field is neither visible to recipients of To: field, nor to recipients of Cc field and not even to the other recipients of Bcc field. |
| Use | It is used to make the primary recipient more serious about the mail. | Use when you don't want to share the list of recipients with other recipients. |
Posted by Ghh Sing 7 years ago
- 1 answers
Abhijeet Soni 7 years ago
Posted by Prajapat Rishabh 5 years, 11 months ago
- 2 answers
Posted by Pubg Hack Make Apptitude Of 7 years ago
- 0 answers
Posted by Vipul Mishra 7 years ago
- 1 answers
Posted by Ayush Yadav 7 years ago
- 0 answers
Posted by Sonu Kumar 7 years ago
- 1 answers
Raghav Gangrade 7 years ago
Posted by Vijay Gupta 7 years ago
- 2 answers
Gaurav Seth 7 years ago
Hackers:
1) Hackers are interested in gaining knowledge about computer systems.
2) These can be for good or bad purposes.
Crackers:
1) These are the malicious programmers who break into secure systems.
2) These are only for bad purposes.
Posted by Sagat Mehndiratta 7 years ago
- 0 answers
Posted by Renu Rani Maurya 7 years ago
- 1 answers
Posted by Raghav Gangrade 7 years ago
- 1 answers
Amarjeet Kaur 7 years ago
Posted by Rajiv Kumar Singh 7 years ago
- 1 answers
Gaurav Seth 7 years ago
Data can be defined as a representation of facts, concepts, or instructions in a formalized manner, which should be suitable for communication, interpretation, or processing by human or electronic machine.
Posted by Crazy Tech With Himanshu 7 years ago
- 2 answers
Amarjeet Kaur 7 years ago
Amarjeet Kaur 7 years ago
Posted by Ankit Chaudhary 7 years ago
- 2 answers
Hiru ? 7 years ago
Posted by Anjali 0123 7 years ago
- 0 answers
Posted by Jasveer Canada Singh 7 years ago
- 0 answers
Posted by Ayush Yadav 7 years ago
- 2 answers
Posted by Adee G. 7 years ago
- 3 answers
Posted by Asmit Raj 7 years ago
- 4 answers
Gaurav Seth 7 years ago
Sir Tim Berners-Lee invented the World Wide Web in 1989. Sir Tim Berners-Lee is a British computer scientist. He was born in London, and his parents were early computer scientists, working on one of the earliest computers.
Posted by Rita Singh 7 years ago
- 3 answers
Posted by Ankush Jaglan 7 years ago
- 2 answers
Ankit Kumar 7 years ago
Posted by Ashok Giri 7 years ago
- 1 answers
Gaurav Seth 7 years ago
| Basic | Controls the white space between the border of a cell and its content. | Sets the space between the solitary cells. |
| Meant for | Single cell | More than one cell |
| HTML format | 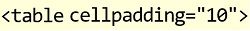 |
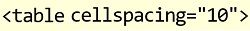 |
Posted by Anurag Pritam 7 years ago
- 2 answers
Posted by Ritika Gupta 7 years ago
- 3 answers
Raj Thakur 7 years ago
Posted by Prashant Chauhan 7 years ago
- 2 answers
Raj Thakur 7 years ago
myCBSEguide
Trusted by 1 Crore+ Students

Test Generator
Create papers online. It's FREE.

CUET Mock Tests
75,000+ questions to practice only on myCBSEguide app
 myCBSEguide
myCBSEguide